As local governments modernize their operations and expand digital services, the need for clear, well-structured roles in IT and cybersecurity has never been more urgent. From online permitting platforms to cloud-based data systems, municipalities are increasingly reliant on technology to deliver public services. But with this reliance comes risk—and the responsibility to manage it effectively.
One of the most important steps in building cyber resilience is clarifying the distinction between IT and cybersecurity functions. While these domains are closely related, they serve fundamentally different purposes and must be structured accordingly.
Why Role Clarity Matters
Strong governance depends on clear role definitions. When IT and cybersecurity responsibilities are blurred, security can be compromised by operational urgency or budget constraints. For example, if a city launches a new online permitting system, the IT team may focus on uptime and user experience, while cybersecurity professionals ensure that sensitive resident data is encrypted, access is controlled, and third-party risks are assessed.
This separation allows cybersecurity teams to assess risk independently and advocate for protections that may not align with short-term operational goals—but are essential for long-term resilience.
Structuring Roles: A Governance-Aligned Approach
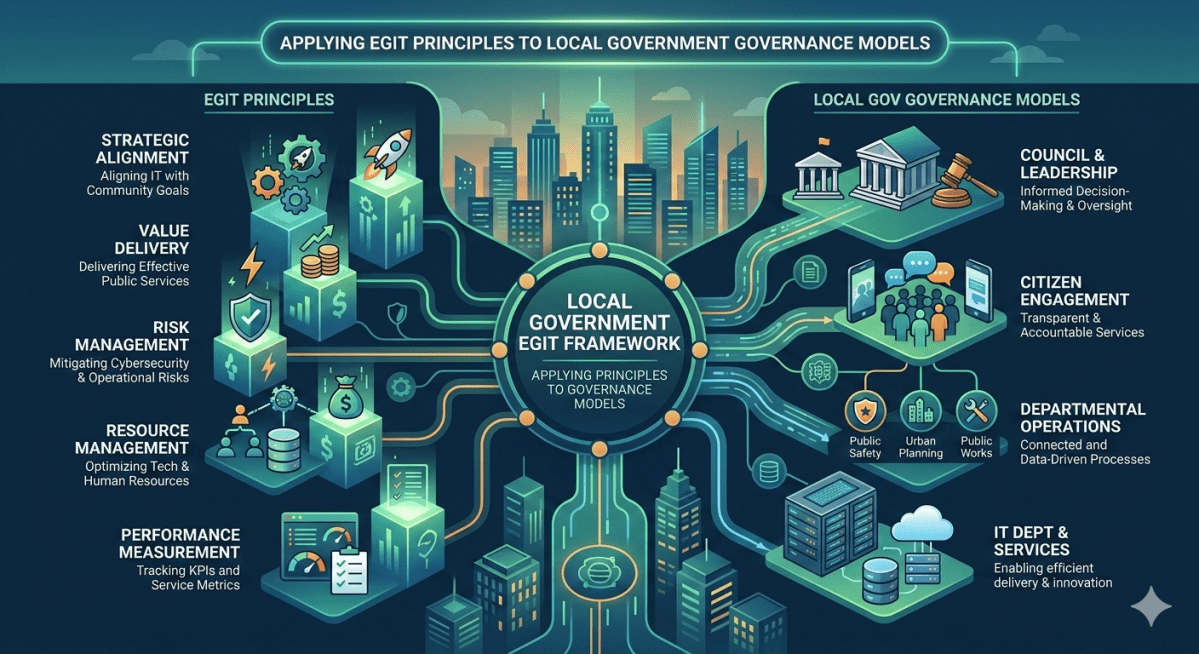
The Enterprise Governance of Information and Technology (EGIT) framework provides a model for structuring IT and cybersecurity roles in a way that supports strategic alignment and risk-informed decision-making.
1. Functional Separation
- IT Departments: Focus on deploying and maintaining technology systems that support operations.
- Cybersecurity Teams: Focus on protecting data, systems, and infrastructure from threats.
This separation ensures that cybersecurity professionals can operate without being subordinated to project timelines or budget pressures.
2. Leadership Accountability
Cybersecurity is not just a technical issue—it’s a leadership responsibility. Elected officials, department heads, and senior executives must recognize that cyber risk affects their ability to deliver services and maintain public trust.
3. Defined Responsibilities Across Roles
Every employee in local government has a role in cybersecurity—from locking devices and reporting suspicious activity to completing training and following data protection protocols.
Examples of Role Definitions
| Role | Primary Focus | Key Responsibilities |
|---|---|---|
| IT Director | Operational technology | System uptime, software deployment, vendor management |
| Cybersecurity Officer | Risk management | Threat detection, incident response, policy enforcement |
| Department Heads | Strategic oversight | Aligning tech use with service goals, ensuring compliance |
| Frontline Staff | Daily operations | Following security protocols, reporting incidents |
Local governments must build governance structures that support both innovation and protection. By clearly defining and separating IT and cybersecurity roles, municipalities can:
- Make unbiased, risk-informed decisions.
- Respond more effectively to threats.
- Build a culture of cybersecurity across all departments.